Combining SonarQube and Azure DevOps
Code analysis is a best practice in a operating continuous integration pipeline. SonarQube can be used in combination with Azure DevOps. If you do not know SonarQube, it is tool that centralizes static code analysis and unit test coverage. It can be used across multiple languages and for a single project up to enterprise scale.
SonarQube
can be used as a SaaS product or hosted on your own instance. SonarQube describes
the product as followed:
SonarQube provides the capability to not only show health of an application but also to highlight issues newly introduced. With a Quality Gate in place, you can fix the leak and therefore improve code quality systematically.
This sound interesting and when useful for your situation it should be placed within a continuous integration pipeline, but how do we get started.
SonarQube Deployment
To get
started with SonarQube I used the installation on an Azure App Service created
by a premium field engineer from Microsoft. The blog post below contains an ARM
template that really makes it a single click install.
- SonarQube
Hosted On Azure App Service - https://blogs.msdn.microsoft.com/premier_developer/2018/12/23/sonarqube-hosted-on-azure-app-service/
What you
might wonder is what the reason was why I used the Azure App Service
deployment:
- No
license needed - You
do not have to create and manage a Virtual Machine. - Setting
up SSL is easier. - You
can easily integrate other Azure services like the Azure Key Vault. - Other
features of the Azure App Service could be used like deployment slots.
Note: When using the “Deploy to Azure” button and you
are using a resource group naming policy you temporary disable it. The “Deploy
to Azure” method uses a test that creates a resource group with a GUID to
validate the template.
Deploying
the resource will not take long. Starting SonarQube is totally different
depending on the hosting platform it can take up to 15 minutes.
When the tooling
is started login with the admin credentials (admin/admin). Make sure you
change them after your first login.
SonarQube Configuration
For sending information to SonarQube a token is needed. To generate a token, click on your name in the top right corner and select “My Account”.
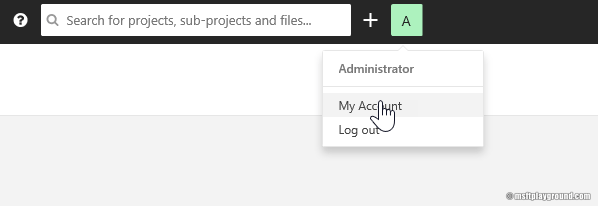
On the “My
Account” screen select “Security”.
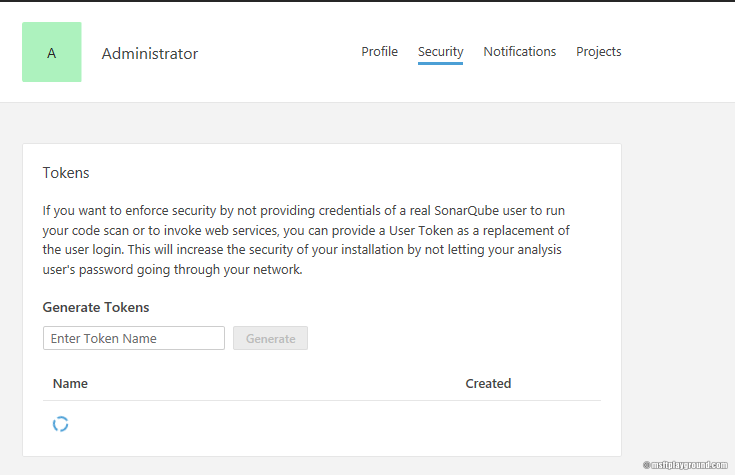
Fill in a
name for the token and click on generate. Copy the token for later use. The
next step is to create a new project within SonarQube. The project will be the
centralized storage for your analytics information of the code. To create a new
project, click on the “+” sign next to your name.
Fill in the
appropriate information and select the main language of your project.
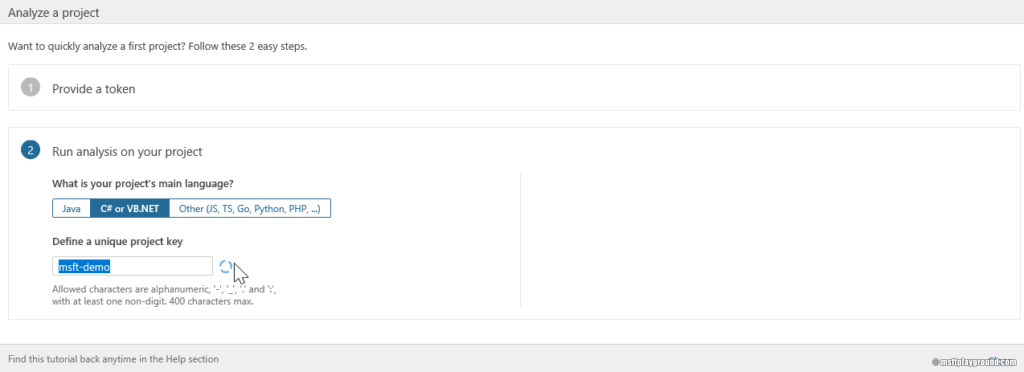
The project
is now ready, and we can start to configure Azure DevOps to send the analysis information
to your SonarQube environment.
Azure DevOps Extension
To make use
of SonarQube within Azure DevOps an extension needs to be installed. Here you
can find the links to the extensions for SonarQube:
- SonarCloud
(SaaS version SonarQube)- https://marketplace.visualstudio.com/items?itemName=SonarSource.sonarcloud - SonarQube
(Hosted version. The version we will use in this blog post)- https://marketplace.visualstudio.com/items?itemName=SonarSource.sonarqube
Build Pipeline
In your Azure
DevOps project create a new pipeline or open a pipeline that you want to extend.
Press the button to add a new task and search for Sonar you will see the
following available tasks. The three-task selected are for the hosted version
of SonarQube.
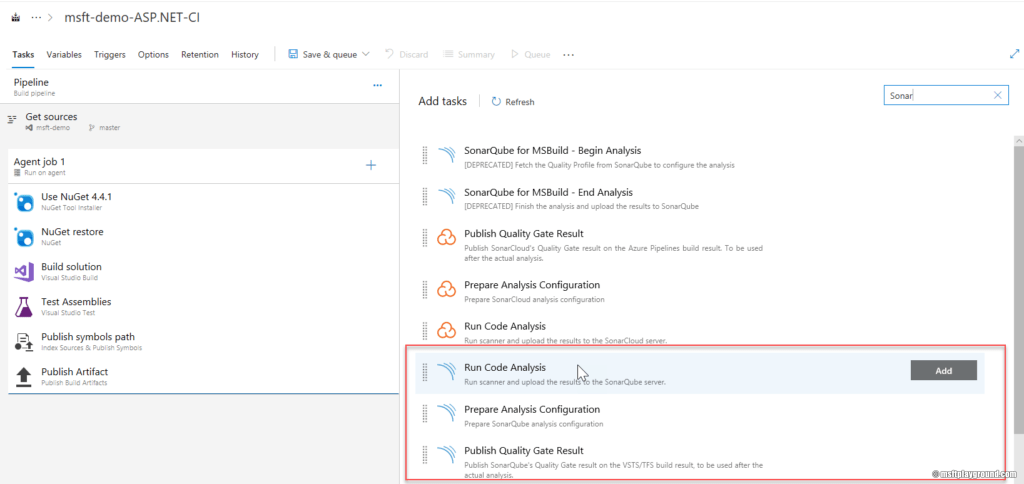
We will
start with the “Prepare Analysis Configuration” then the “Run Code Analysis”
and then the “Publish Quality Gate Result”.
Prepare Analysis
Configuration
The
“Prepare Analysis Configuration” is the most important task. With this task you
configure the agent job to work correctly with SonarQube.
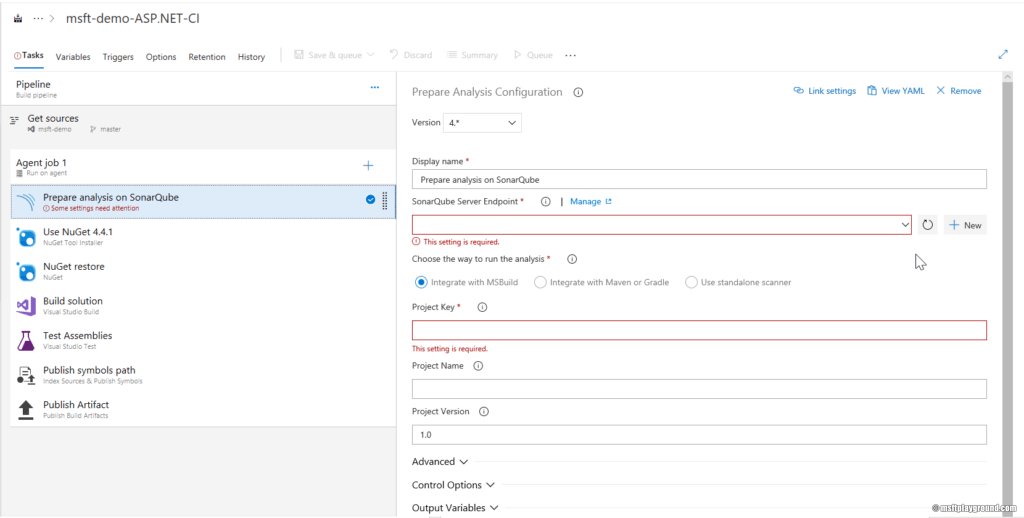
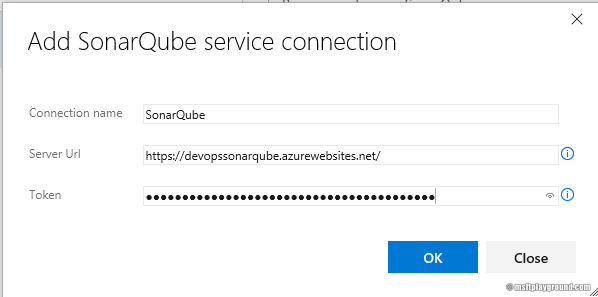
To
establish the connection the tasks needs a SonarQube service endpoint. To
create a new service endpoint for SonarQube you can click on the “New” button. In
the configuration window for this endpoint fill in the correct information.
In the task
itself fill in the key of the project and the name. The task is now configured this
means the other tasks can be added to the pipeline. The other task itself do
not have any additional configuration.
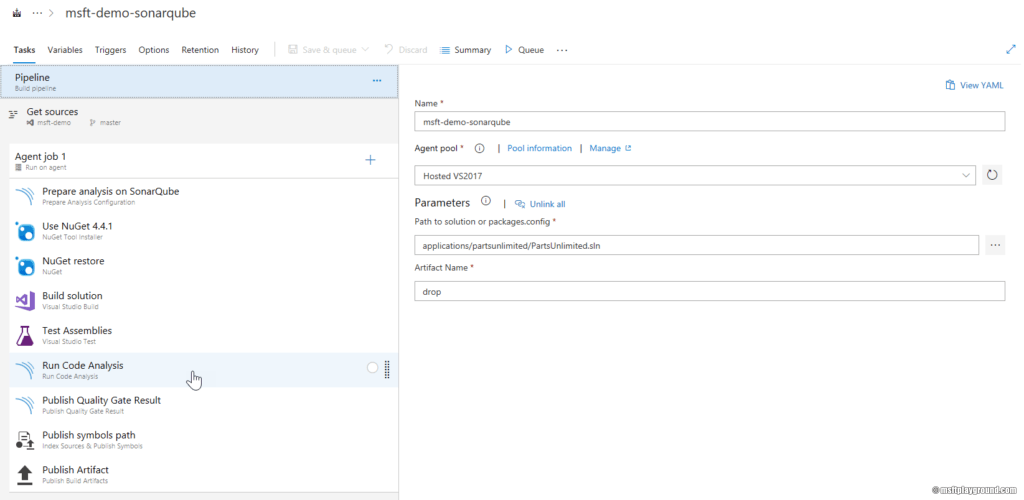
If you want
to include test result you need to make sure to add the “Run Code Analysis”
task after the “Test Assemblies” task like the screenshot above.

In the
upcoming days and weeks, I will check more functionality and will share more information
on this blog.

Comments