Custom Self Signed Certificate Identity Server
For Identity server to be able to sign the login request you can add a Test certificate from the Identity Server it self or you are able to generate a certificate your self.
Generate certificate
To generate a certificate compatible for Identity Server your self you can perform the following command in a “Developer Command Prompt”.
C:\Temp>makecert -r -pe -n "CN=MSFTPlayground" -b 01/01/2015 -e 01/01/2099 -eku 1.3.6.1.5.5.7.3.3 -sky signature -a sha256 -len 2048 -ss Personal -sr LocalMachine
The command will generate a self signed certificate within your local computer certificate store.
Once generated you can export the certificate including the private key with the MMC-snapin.
- Open a Command Prompt window, in Administration Mode.
- Type mmc and press the ENTER key.
- On the File menu, click Add/Remove Snap In.
- Click Add.
- In the Add Standalone Snap-in dialog box, select Certificates.
- Click Add.
- In the Certificates snap-in dialog box, select Computer account and click Next.
- In the Select Computer dialog box, click Finish. (by default it will use “Local Computer”)
- In the Add Standalone Snap-in dialog box, click Ok.
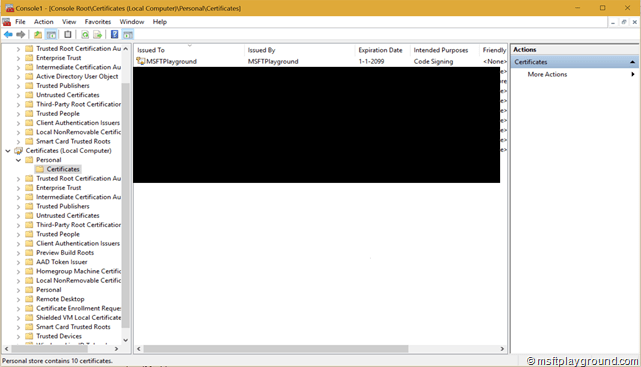
Within the Personal folder open the Certificates. Within that container you can see your certificate.
PowerShell
As many of you may know the makecert application is deprecated. The new option to generate certificates is using PowerShell. With the method “New-SelfSignedCertificate” it is quite hard / pretty impossible to generate this kind of certificates.
Vadims Podans created a helpful PowerShell extension for creating advanced certificates. The PowerShell extension can be downloaded from here:
This will leaves you with implementing the following PowerShell script.
.\New-SelfSignedCertificateEx.ps1 New-SelfsignedCertificateEx -Subject "CN=MSFTPlayground" -EKU 1.3.6.1.5.5.7.3.3 -KeySpec "Signature" -KeyUsage "DigitalSignature" -SignatureAlgorithm "SHA256" -KeyLength 2048 -FriendlyName "MSFTPlayground Code Signing" -NotAfter $([System.DateTime]::Now.AddYears(15)) -Exportable

Comments